this article outlines the key ideas for achieving cross-regional traffic distribution and high availability in taiwan's multi-site cluster environment, covering solution selection (such as dns/gslb, anycast, cloud lb), implementation methods of network and session persistence, health check and monitoring locations, compliance and delay considerations, as well as implementation considerations such as disaster recovery switching and drills. it aims to help network and operation and maintenance teams strike a balance between cost, performance and reliability.
how many nodes or computer rooms need to be considered for deployment?
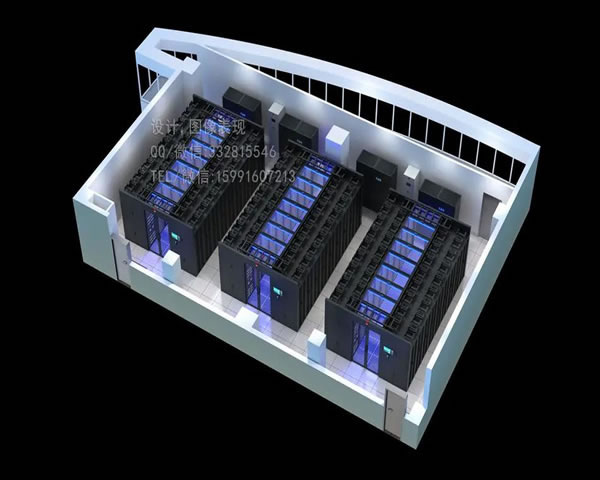
when planning cross-region load balancing , you should first evaluate access source distribution and business delay tolerance. for the taiwan scenario, at least 2 availability zones (north and south or different telecom operators) are usually required to achieve redundancy; if it is for overseas users, overseas nodes are added to optimize latency. the number of nodes is determined by the traffic peak, disaster recovery strategy and cost. it is recommended to adopt a capacity plan (capacity + 30% redundancy) and calculate according to ttp (traffic, throughput, performance).
which load balancing solution is more suitable for taiwan group stations?
common solutions include dns-based gslb, ip anycast+bgp, and regional load balancing provided by cloud vendors. if you pursue global intelligent scheduling and weight control, you can use gslb combined with health detection; if you pursue the shortest route and low latency, you can use anycast with edge nodes. for projects with quick launch and simple operation and maintenance, cloud lb+cdn is a common compromise. when choosing, you need to weigh switching speed, session consistency, and operation and maintenance complexity.
how to implement traffic scheduling and session maintenance in taiwan group station?
to achieve session persistence, you can use four-layer source address stickiness, five-layer cookie stickiness, or implement distributed session storage (such as redis) at the application layer. when using cross-region load balancing , try to limit stickiness control to the same availability zone, and use the gslb policy to perform read-write separation or active-standby switching between nodes. ssl certificates should be centrally managed and support ocsp/automatic renewal to ensure that user requests are not affected when switching.
where is the best place to place health inspections and monitoring?
health checks should exist at both the edge (load balancer) and the intranet (backend instance): edge inspection quickly determines the direction of traffic, and intranet inspection ensures that the service logic and dependency chain are normal. the monitoring system needs to cover response time, error rate, bandwidth and number of connections, and combine synthetic monitoring to perform end-to-end detection of user paths. logs and indicators should be collected centrally (prometheus/elk) and set up hierarchical alarms.
why should you pay special attention to compliance and network latency issues?
taiwan has specific operational and privacy requirements for telecommunications and data storage, and some industries may require data residency or specific qualifications to exchange traffic. in addition, the interconnection point between the submarine cable and the operator will affect the round-trip delay, and it is necessary to use multiple operators or local interconnection points (ix) to reduce the risk of jitter and single point failure. when designing taiwan cluster server deployment , compliance review and link diversification are must-dos.
how to conduct failover and drills to ensure availability?
formulate a clear rto/rpo, establish an automated failover mechanism (such as gslb weight reduction, bgp routing revocation, or dns short ttl switching strategy), and conduct regular full-link drills (including capacity burst, single point failure, and rollback processes). the results of the drill should be fed back into the runbook and sla indicators to ensure that the team can quickly recover in steps when a real failure occurs.
- Latest articles
- The Impact Of Long-term Subscription And On-demand Billing On Japanese Cn2 Prices And Comparison Methods
- A Quick Tutorial On Setting Up A Demo Environment And Using Vps Hong Kong Hosting Free Plan
- The Official Website Of Cera In The United States Does Not Have The Potential Impact Of Cn2 On The Access Experience Of Global Users.
- Evaluation Of The Stability Of Malaysian Vps With Unlimited Traffic Under Long-term High Concurrency Environment
- How To Verify The Validity And Usage Restrictions Of Singapore Vps Vouchers
- Compare The Differences Between Cloud Vendors To Help You Decide On The Cost Performance And Services For Renting A Vps Host In The United States
- Amazon Japan Site Group Revenue Model Decomposition Pricing Strategy And Promotion Ratio Suggestions
- Practical Guide To Taiwan's Three-network Direct-connect Vps Line Selection And Load Balancing Configuration
- Full Analysis Of The Actual Performance And Optimization Suggestions Of Cn2 Malaysia Lines In Cross-border Acceleration
- Hong Kong Native Residential Ip Compliance Risks And Operator Certification Requirements
- Popular tags
-
Travel Guide And Recommended Attractions For The Yangmingshan High Speed rail Station Group
explore the travel guide and recommended attractions of yangmingshan high-speed railway station group, and enjoy the beautiful natural scenery and rich cultural experience. -
Explore The Advantages And Application Scenarios Of Taiwan's Original Ecological Ip
this article deeply explores the advantages and application scenarios of taiwan's original ecological ip, and combines the performance evaluation of the server to provide users with the best choice suggestions. -
Key Points In The Construction Of Monitoring System And Automatic Recovery Process For Long-term Operation And Maintenance Of Native Static Ip In Taiwan
focusing on the long-term operation and maintenance of native static ip in taiwan, we answer five key questions about monitoring indicators, alarm classification, data collection and storage, automatic recovery process construction and verification, as well as long-term governance and security attention points, and provide executable points and practical suggestions.


